Guiding you through life’s financial journey
Compare rates, crunch numbers and get expert guidance for life’s biggest financial moments.
The Bankrate Award winners are here
Skip the searching and find the top financial products of 2024, all in one spot. From insurance companies to investment accounts, we've got you covered with our top picks in every category.

Bankrate recommends
Introducing Whole Human Finance™
With the help of National Debt Relief, you can reduce your debt and empower yourself to find help for your entire situation – not just your bank account.

10 best investments in 2024
These top investments offer your portfolio the potential for steady, positive returns.
Get out of debt with the best companies of 2024
How many business credit cards should I have?
Find the right credit card for your venture as a small business owner to help you achieve your goals.
Exclusive insights from our expert analysts
“There are plenty of ways to have fun this summer without busting your budget. For example, there’s still time to accumulate a summer vacation fund by setting money aside from every paycheck.”

36% of Those Planning Summer Vacations Willing to Go Into Debt For Their Travels



Find answers, fast
A better rate is waiting
National average banking rates
| 1 Year CD | 1.75% | |
| 3 Year CD | 1.41% | |
| 5 Year CD | 1.43% | |
| Savings Account | 0.57% |
Current mortgage rates
| 30 Year Fixed | 7.23% | |
| 15 Year Fixed | 6.70% | |
| 10 Year Fixed | 6.54% | |
| 5/1 ARM | 6.68% |

Trusted news and reviews, published daily
See all newsReviews and recommendations
Advertiser disclosureBankrate independently researches financial companies and rates them according to an objective set of criteria. For more information on how we stay impartial, check out our editorial integrity policy.
Reviews by category
REVIEWS OF TOP BANKS
REVIEWS OF TOP MORTGAGE LENDERS
Popular topics
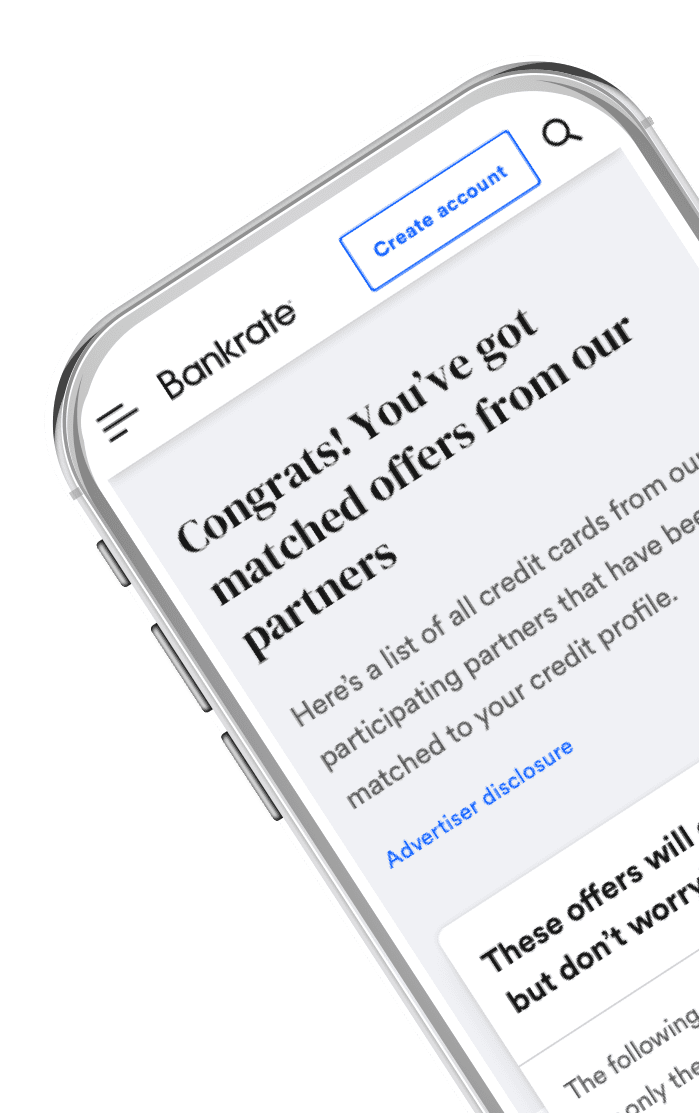
Introducing Cardmatch™ Your perfect card is one click away
Find your matchWhy CardMatch™?
-
1
No impact to your credit score
-
2
Bank-level security to keep your data safe
-
3
Elevated bonus offers and custom results